Equifax Insider Trading Charges Highlight Importance of Tailored Policies and Controls
Equifax Insider Trading Charges Highlight Importance of Tailored Policies and Controls
By Trudy-Anne McLeary, Associate
In what appears to be the first insider trading case stemming from insider knowledge of material nonpublic cyber-related information, the Securities and Exchange Commission brought civil charges against a former Equifax executive, alleging that the executive illegally traded on the basis of information from which he deduced that Equifax had suffered a major data breach.
On March 14, 2018, the Securities and Exchange Commission (the Commission) filed a federal civil complaint in the Northern District of Georgia against the former chief information officer (CIO) of Equifax’s U.S. Information Systems business unit. The complaint charges the former CIO with insider trading in violation of federal securities law, alleging that the CIO determined that Equifax was the victim of a major data breach based on confidential information entrusted to him by the company and thereafter proceeded to trade stock in advance of a public announcement of the breach.
The Commission’s complaint comes just three weeks after it released a statement and interpretive guidance (the Guidance) expressing its continued interest in and heightened scrutiny of public companies’ cybersecurity disclosures as well as oversight and compliance obligations, including insider trading policies and procedures.
Overview of the Guidance
The Guidance, released by the Commission on February 21, 2018, reinforces and expands on earlier guidance regarding cybersecurity disclosures issued by the Commission’s Division of Corporate Finance in October 2011 (the 2011 Release). In relation to the issuance of the Guidance, Commission Chairman Jay Clayton stated that “providing the SEC’s views on these matters will promote clearer and more robust disclosure by companies about cybersecurity risks and incidents, resulting in more complete information being available to investors.”
While much of the Guidance builds on the Commission’s 2011 Release and reiterates the importance of timely disclosure, the Guidance is particularly important because of its discussion of two topics not previously developed: (1) the significance of adopting and maintaining comprehensive cybersecurity policies that address the sufficiency of disclosure controls and procedures and (2) the application of insider trading prohibitions in the context of cybersecurity.
Disclosure Controls and Procedures
The Guidance underscores the crucial role of comprehensive disclosure controls and procedures that can both guide a company in its effective evaluation of the impact that cybersecurity matters have on various aspects of the company’s operation and create a protocol by which a company can analyze the materiality of such concerns. Specifically, the Guidance advises that “[w]hen designing and evaluating disclosure controls and procedures, companies should consider whether such controls and procedures will appropriately record, process, summarize, and report the information related to cybersecurity risks and incidents that is required to be disclosed in filings.” Importantly, the Guidance states that such disclosure controls and procedures should ensure that relevant information regarding cybersecurity risks and developments is escalated to the right personnel in the company in order to facilitate the certifications that must be made by management regarding the design and effectiveness of such controls and procedures. This suggests that companies will want to adopt and implement cybersecurity risk management policies that identify disclosure controls and procedures to ensure that risks and incidents are timely identified, evaluated and reported appropriately. The Commission specifically notes that these policies should be regularly assessed in order to ensure their compliance with federal securities law. Where necessary to supplement internal resources, companies should consider consulting with technical experts and advisers regarding their certification and disclosure committee procedures.
Insider Trading Policies
The Guidance emphasizes that knowledge of major cybersecurity risks and incidents may well be material nonpublic information, and therefore should be treated as such in insider trading policies. Thus, companies will want to consider specifically referring to cybersecurity risks and incidents when defining what constitutes “material nonpublic information” in their codes of ethics and insider trading policies, in order to make clear that knowledge of such events may qualify as material nonpublic information in the context of insider trading. The Guidance also encourages companies to consider whether and when it may be appropriate to place restrictions on insider trading during the investigation of significant cybersecurity incidents.
The Commission’s Complaint Alleging Insider Trading
The Commission’s recent complaint provides context to the Commission’s discussion of insider trading in the Guidance. The complaint makes it clear that company insiders will want to be mindful of the fact that knowledge of cybersecurity-related information, such as information similar to that about the major Equifax breach, is likely material nonpublic information.
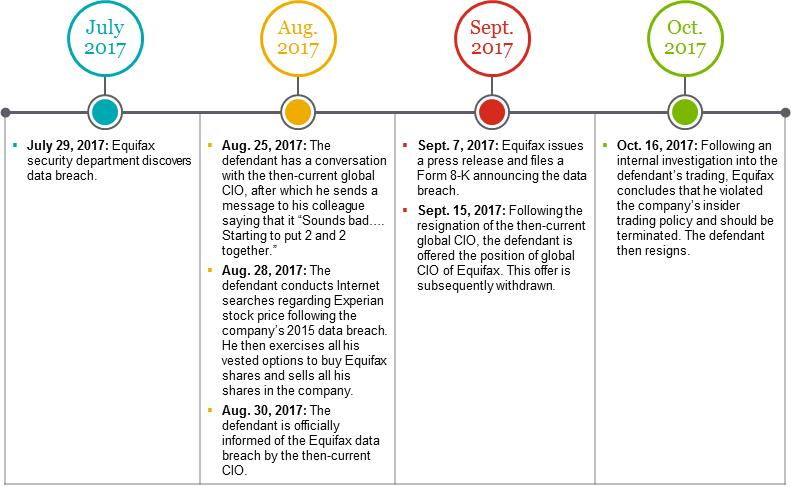
In the complaint, the Commission alleges that shortly after Equifax’s security department became aware of the company’s 2017 data breach, the company formed a response team designated as Project Sierra, comprising security, legal and information technology personnel. Personnel belonging to the Project Sierra response team were instructed not to share the confidential information to which they would become privy with anyone outside of Project Sierra. Based on the confidential information they would receive, Equifax also implemented a special trading blackout period for those working on Project Sierra.
As alleged in the complaint, Equifax also established a notification and remediation plan designated as Project Sparta, which was kept separate from Project Sierra. In an effort by the company to limit the number of people who had knowledge of the data breach, personnel assigned to Project Sparta, which included the defendant, were not told that Equifax had suffered a large data breach. Instead, they were made to believe that they were assisting an unnamed client that had experienced a breach. Importantly, those working on Project Sparta were not subject to a trading blackout period, as were those working on Project Sierra.
The complaint alleges that the defendant engaged in a series of communications with various colleagues, through which he came to the conclusion, based on the information that he received from various sources, that Equifax was the victim of the data breach to which Project Sparta personnel had been assigned. In particular, following a conversation with the then-current global CIO, the defendant allegedly sent a text message to his direct report at the company, stating that he was “[o]n the phone with [global CIO]. Sounds bad. We may be the one breached.… Starting to put 2 and 2 together.” Following this determination, the defendant allegedly conducted Internet searches regarding the 2015 Experian data breach and the effect the breach had on Experian’s stock price. Shortly thereafter, the complaint alleges, the defendant proceeded to exercise all of his vested options to purchase Equifax shares and sold them on the open market prior to any public disclosure of the data breach, thereby avoiding a loss of approximately $117,000.
The defendant, who had been offered the position of Equifax’s next global CIO following the resignation of the then-current global CIO in the wake of the data breach, resigned after the company discovered his trading activities that were in violation of the company’s insider trading policy and concluded he should be terminated.
 1
1
Important Takeaways
The Commission’s Guidance and its more recent civil complaint together emphasize that public companies should implement appropriate policies and procedures that ensure adequate disclosure of material cybersecurity matters and prevent insiders from trading on material nonpublic information related to cybersecurity risks and incidents.
- Companies should carefully review blackout periods to ensure that they are broad enough in scope and that they cover all personnel who are aware or are reasonably likely to become aware of material nonpublic information. In the Guidance, the Commission advises that companies would be “well served by considering the ramifications of directors, officers, and other corporate insiders trading in advance of disclosures regarding cyber incidents that prove to be material.” The complaint squarely brings this warning to the forefront. The special trading blackout period implemented by Equifax shows that companies are at risk if such trading blackouts are too narrowly applied. In the event of a material cyber event, companies should therefore consider expanding blackout periods broadly enough to cover personnel who might indirectly become aware of material nonpublic information. In particular, high-level executives, such as the defendant in the Commission’s complaint, who will play a key role in remediating any cyber incident, should likely be subject to trading blackout periods as a result of the sensitive information to which they will be exposed.2
- Companies will also want to consider reviewing the preclearance provisions of their insider trading policies to ensure that the procedure for defining or identifying designated persons who must obtain approval prior to trading the company’s stock is adequately broad. The defendant, for example, does not appear to have been subject to preclearance despite his seniority and the fact that he worked closely with personnel who had knowledge of the data breach. As such, he was able to freely dispose of his stock, and Equifax did not become aware of his trading activities until several weeks thereafter.3
- Companies should review their insider trading policies to ensure that they specifically include cyber-related matters as one of the types of material nonpublic information on the basis of which the trading of securities is prohibited. Additionally, insider trading policies should be accompanied by adequate training that explores various scenarios under which the sale of company stock may be in violation of the policy and explains the risks and ramifications of trading on material nonpublic information.4
- Companies should consider the adequacy of their existing disclosure controls and procedures related to cybersecurity matters, in particular regarding timely escalation of risks and events. In some cases, companies may need to engage technical experts to assist in creating policies tailored to their unique risk profiles.
- In addition to policies and controls, companies should not forget that timely disclosure in SEC filings is a critical element of an overall approach to cyber events.
Final Thoughts
The Commission’s Guidance has reiterated a message regarding the disclosure of cybersecurity-related matters: “It is critical that public companies take all required actions to inform investors about material cybersecurity risks and incidents in a timely fashion.” The civil complaint, hard on the heels of the Guidance, illustrates the relevance of the Guidance and demonstrates the Commission’s scrutiny of the intertwined issues of cybersecurity, insider trading and disclosure controls. Viewed in tandem, the Guidance and the complaint provide the beginnings of a road map to understanding the risks in this area and potential solutions. In commencing the Equifax civil action, the Commission has certainly made clear its belief that cybersecurity incidents may well constitute material nonpublic information, but perhaps more important, it has illustrated the real-world challenges of securities compliance in the midst of responding to cyber and other major incidents.
We expect that the Commission will continue to examine cybersecurity disclosure and compliance obligations as it analyzes the sufficiency of the disclosures that it receives in light of its Guidance. We will continue to watch the development of the Commission’s case, as well as further developments in this area.
Related Links
Complaint, Securities and Exchange Commission v. Jun Ying, No. 1:18-CV-01069(CAP) (N.D. Ga., March 14, 2018), available at https://www.sec.gov/litigation/complaints/2018/comp-pr2018-40.pdf
Securities and Exchange Commission, “Commission Statement and Guidance on Public Company Cybersecurity Disclosures” (Feb. 21, 2018), available at https://www.sec.gov/rules/interp/2018/33-10459.pdf
Securities and Exchange Commission, “CF Disclosure Guidance: Topic No. 2” (Oct. 13, 2011), available at https://www.sec.gov/divisions/corpfin/guidance/cfguidance-topic2.htm
1A brief summary of the timeline of the defendant’s actions, as alleged and described in the Commission’s complaint.
2The piecing together of bits and pieces of information into “material nonpublic information” can also occur outside of the cybersecurity context. When designing compliance policies, and especially when imposing situation-specific blackouts, companies should be mindful of the Equifax complaint whenever sensitive events (whether or not related to cybersecurity) occur.
3Companies that more or less automate employees’ ability to exercise stock options and execute trades—for example, by having standing arrangements with brokerage firms—may want to look even harder at this issue, since the speed of execution compresses the time frame for the company to take remedial or preventive action.
4For example, executives or other employees might misinterpret the lack of a blackout, and perhaps mistakenly believe that it grants immunity. While nearly every insider trading policy explains that trading is prohibited even in an “open window” if the trader has material nonpublic information, the alleged facts in the Equifax case are a warning of what can happen if this principle is not complied with.
